Wireless G Network Setup for Endpoint Security: A Comprehensive Guide
Wireless G Network Setup for Endpoint Security is an essential aspect of protecting your business from emerging cyber threats. With the increasing reliance on wireless connectivity, securing endpoint devices is crucial to prevent unauthorized access and data breaches. In this article, we will delve into the details of setting up a secure Wireless G Network and discuss the best practices for endpoint security.Traditional Network Appliances and Endpoint Security
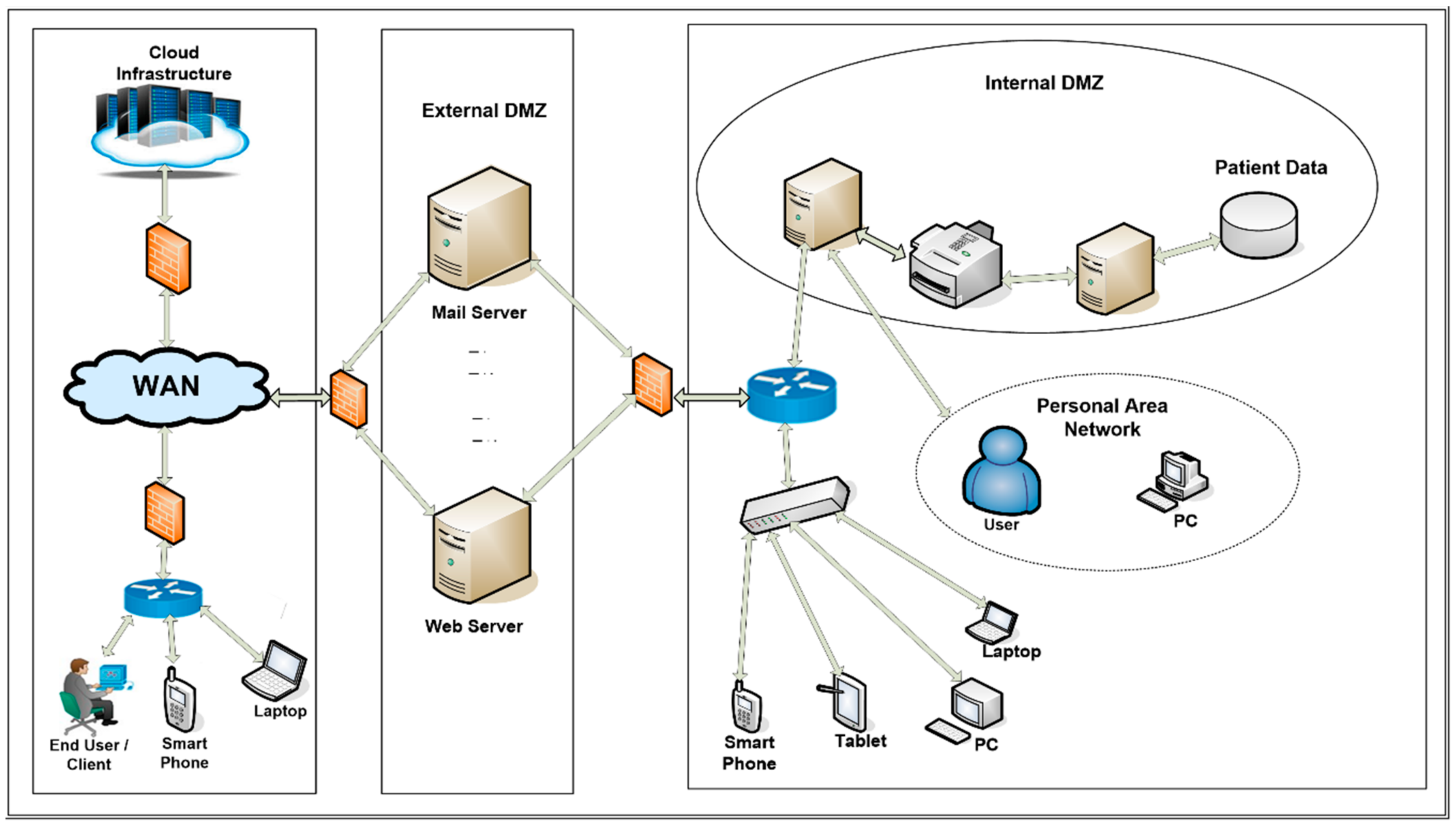
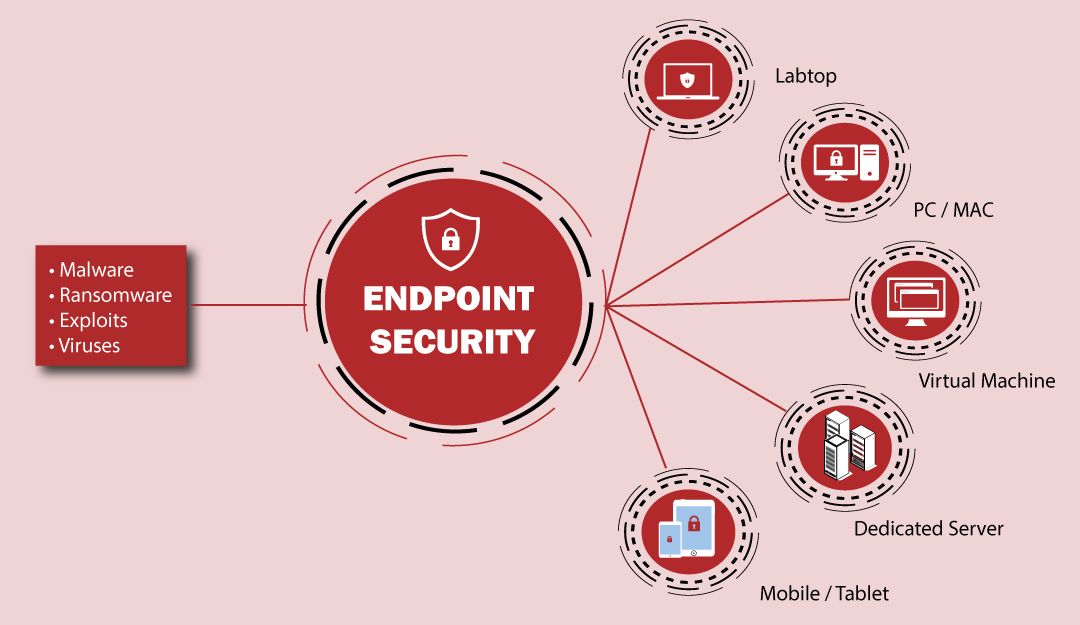
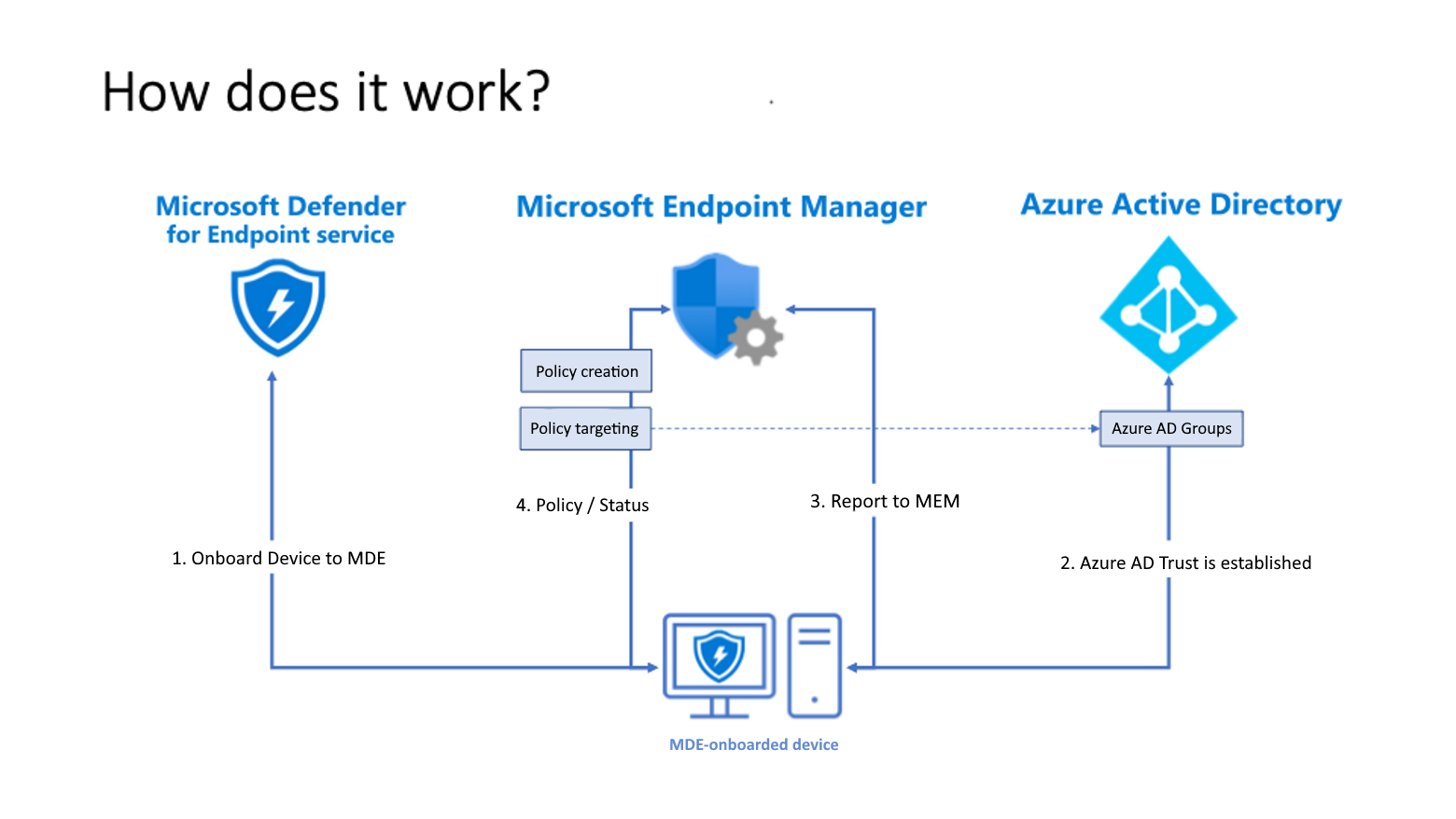
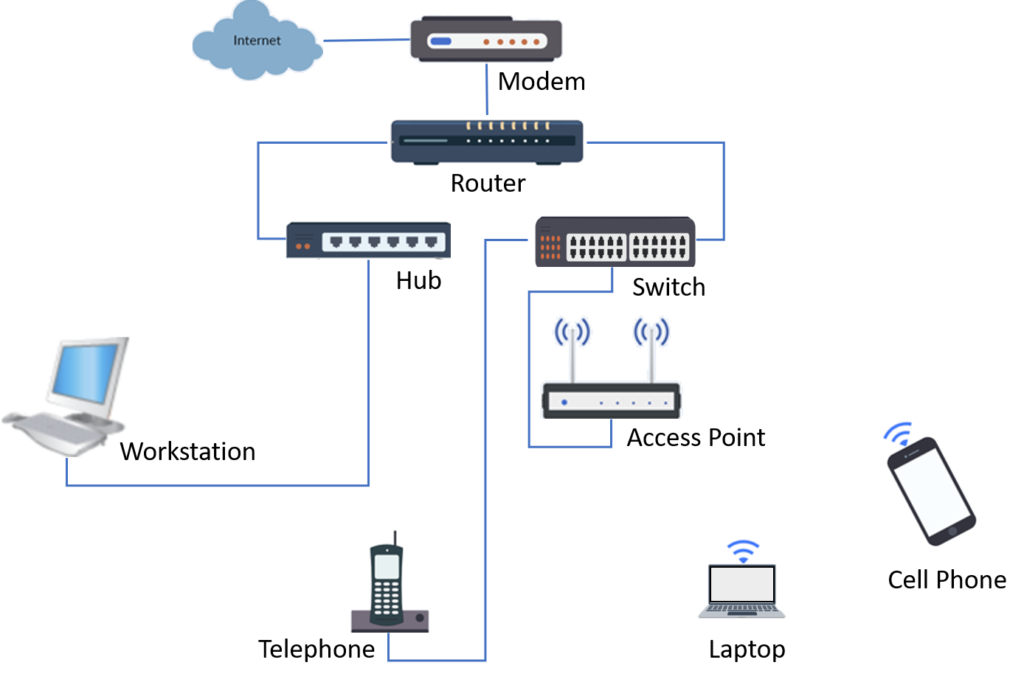
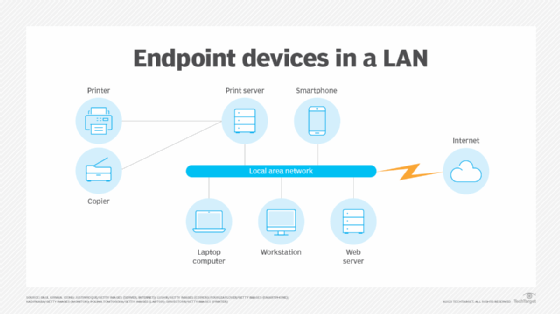
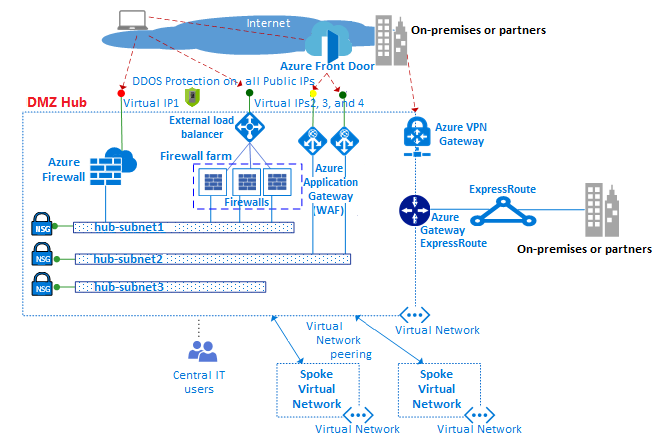
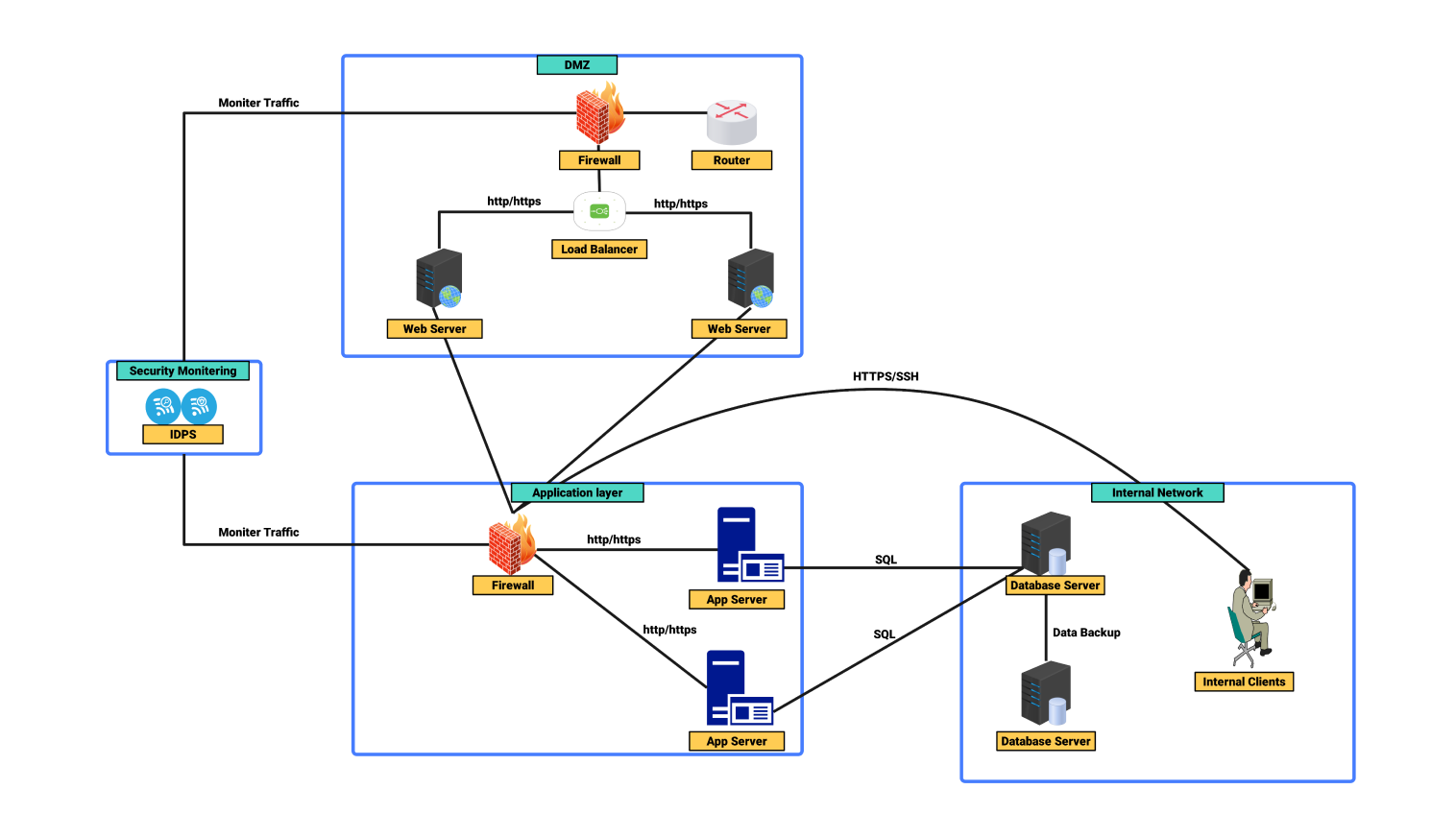
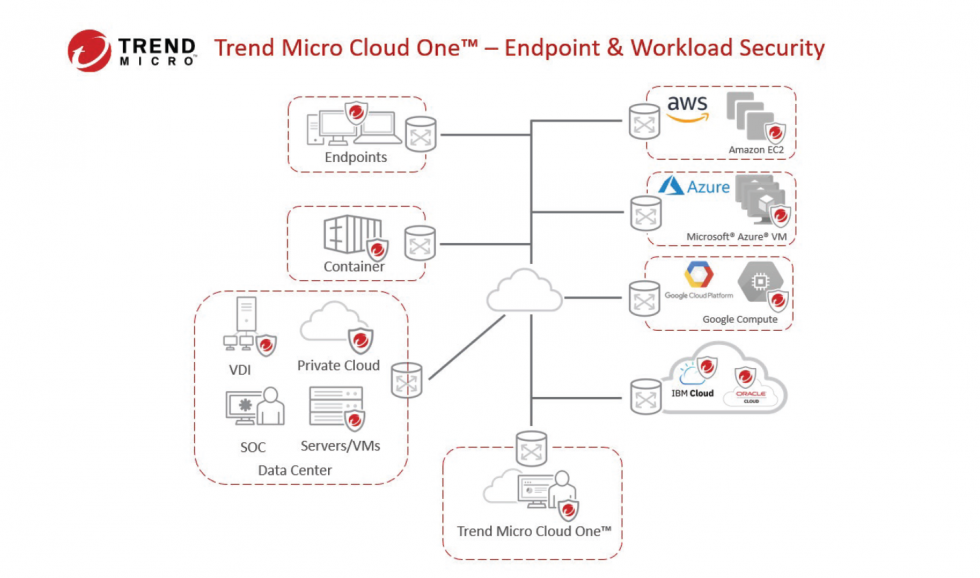
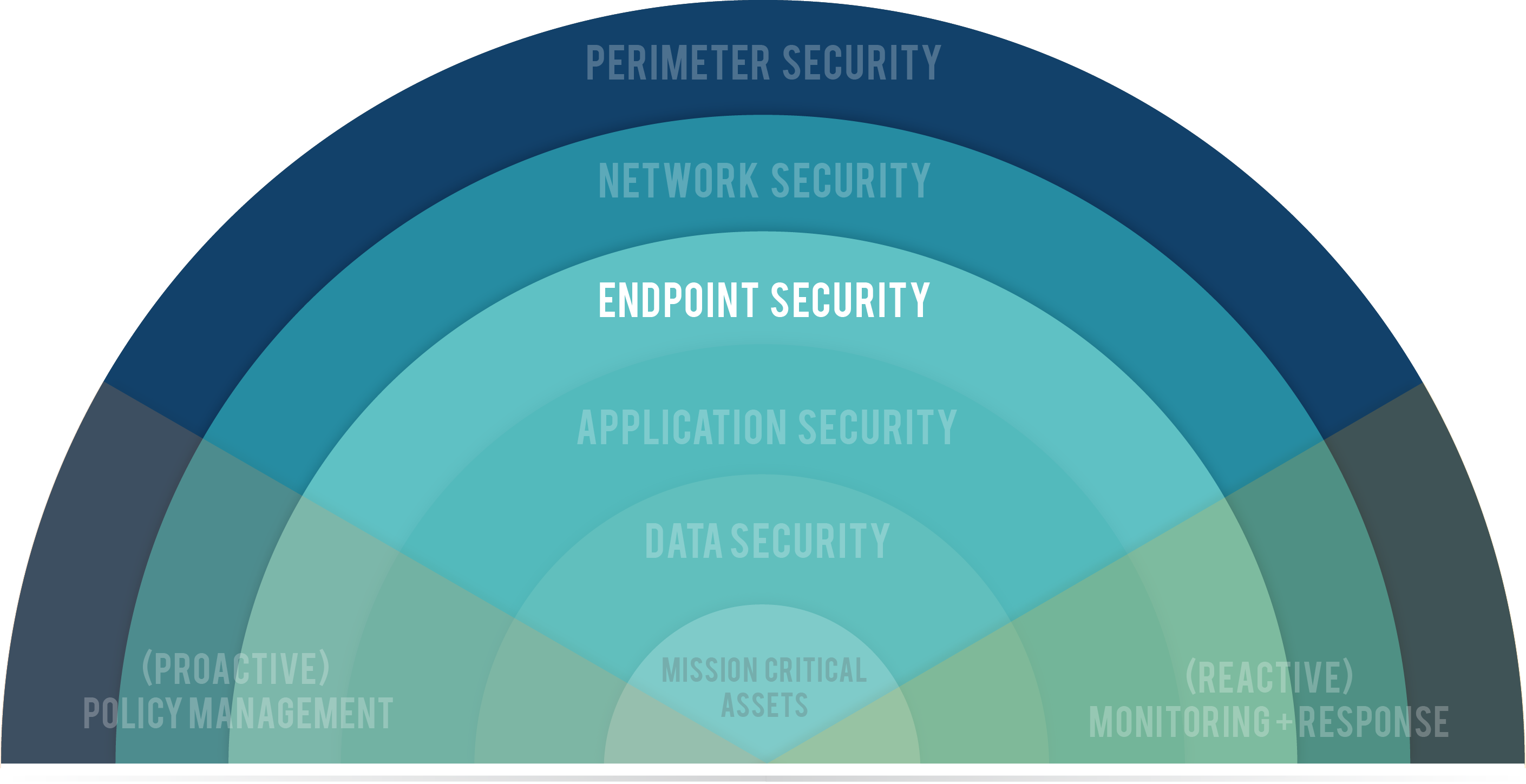
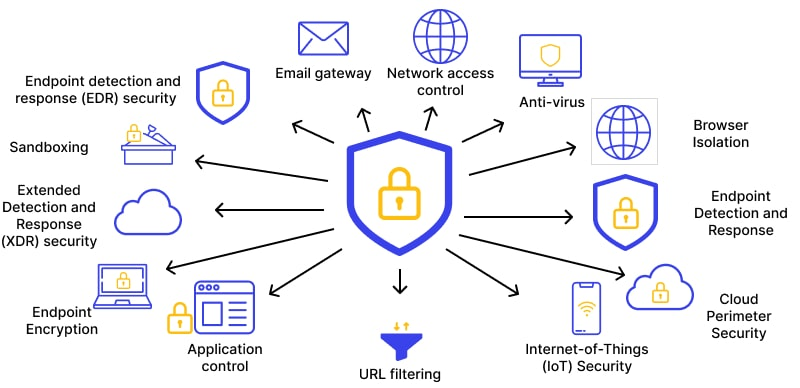
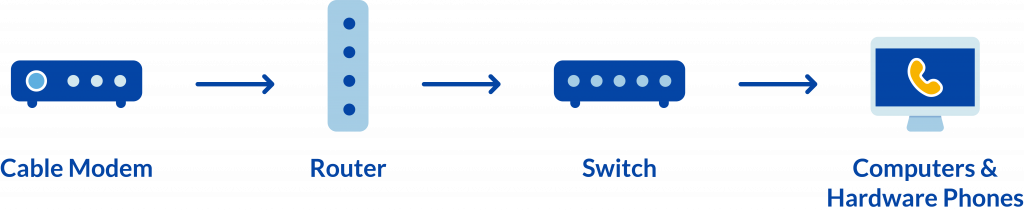
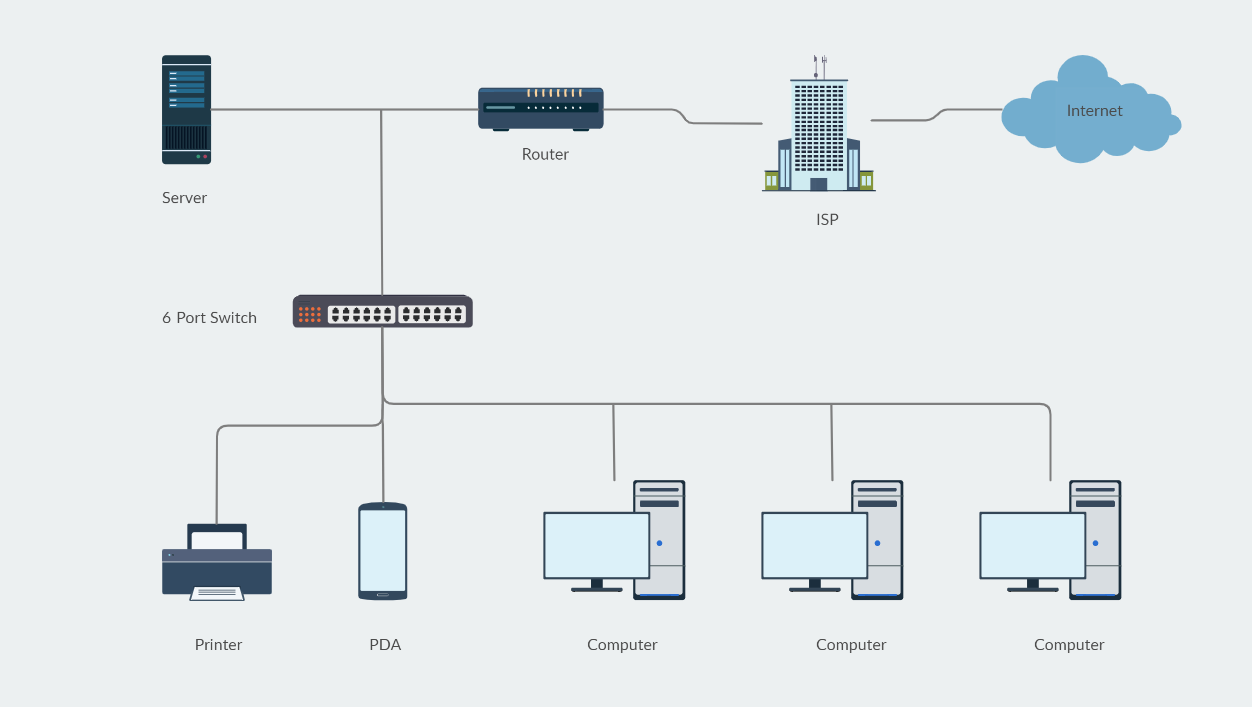
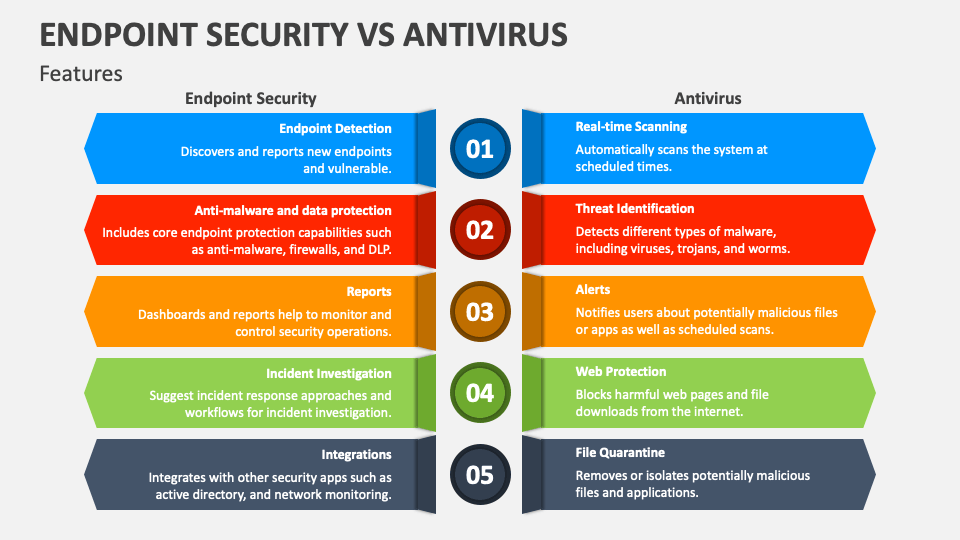
Traditionally, network appliances have focused on enhancing security features through point solutions and network configurations. These solutions often include application/service security, cloud services access security, and device/end-point security. However, with the growing complexity of networks, it is essential to integrate these individual network features into a cohesive security framework.Enhancing Security Features with Wireless G Network Setup
Secure the Network, Secure the Client, Secure the Air
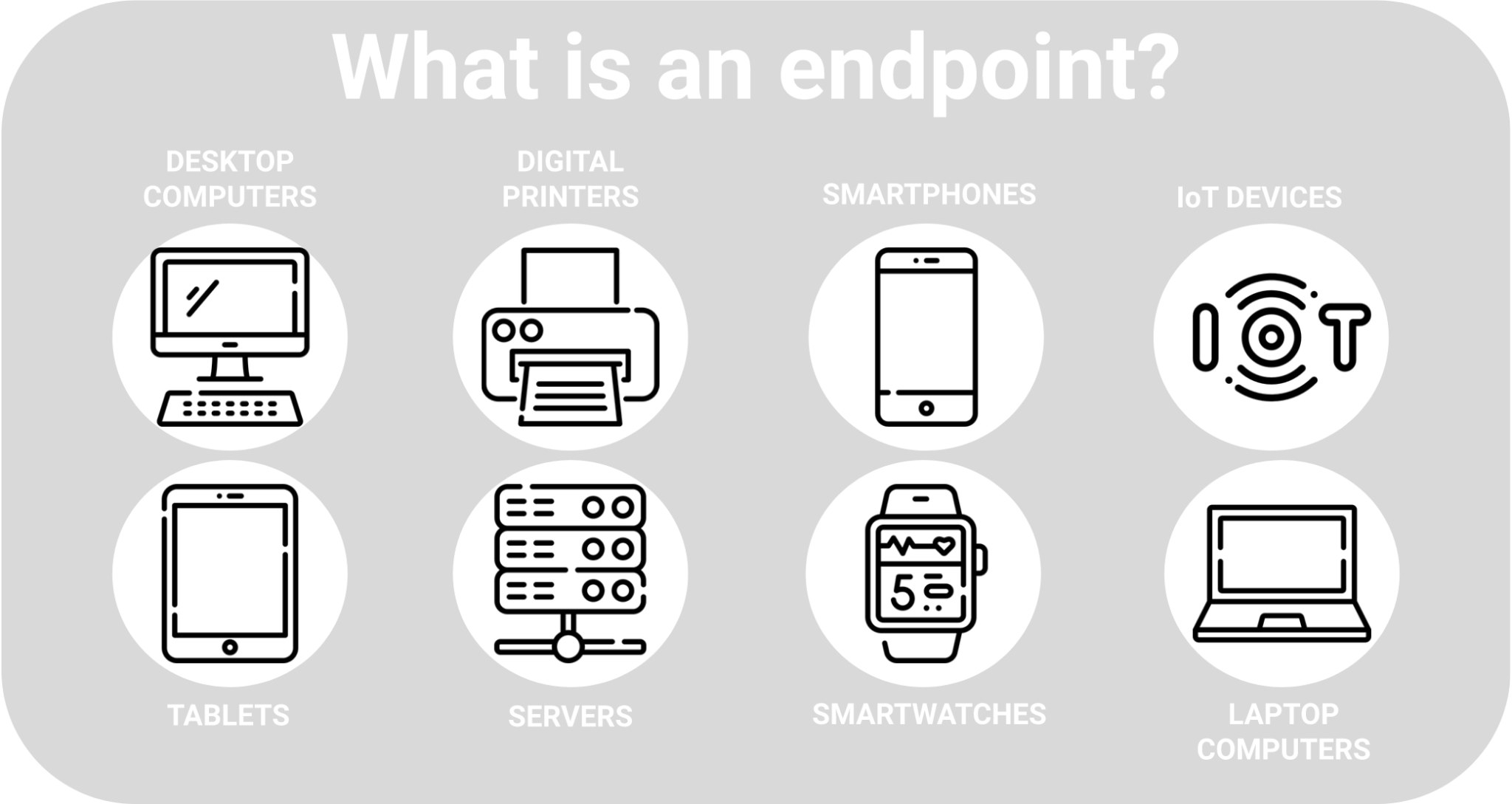
Wireless network security involves securing not only the network but also the client devices and the airwaves. A comprehensive security strategy should include: * Secure the Network: Implementing encryption, client authentication, and access control to ensure secure data transmission * Secure the Client: Providing application visibility and monitoring to detect and prevent malicious activities * Secure the Air: Implementing Wireless Intrusion Prevention Systems (WIPS), rogue detection, and containment to prevent unauthorized accessBest Practices for Wireless G Network Setup
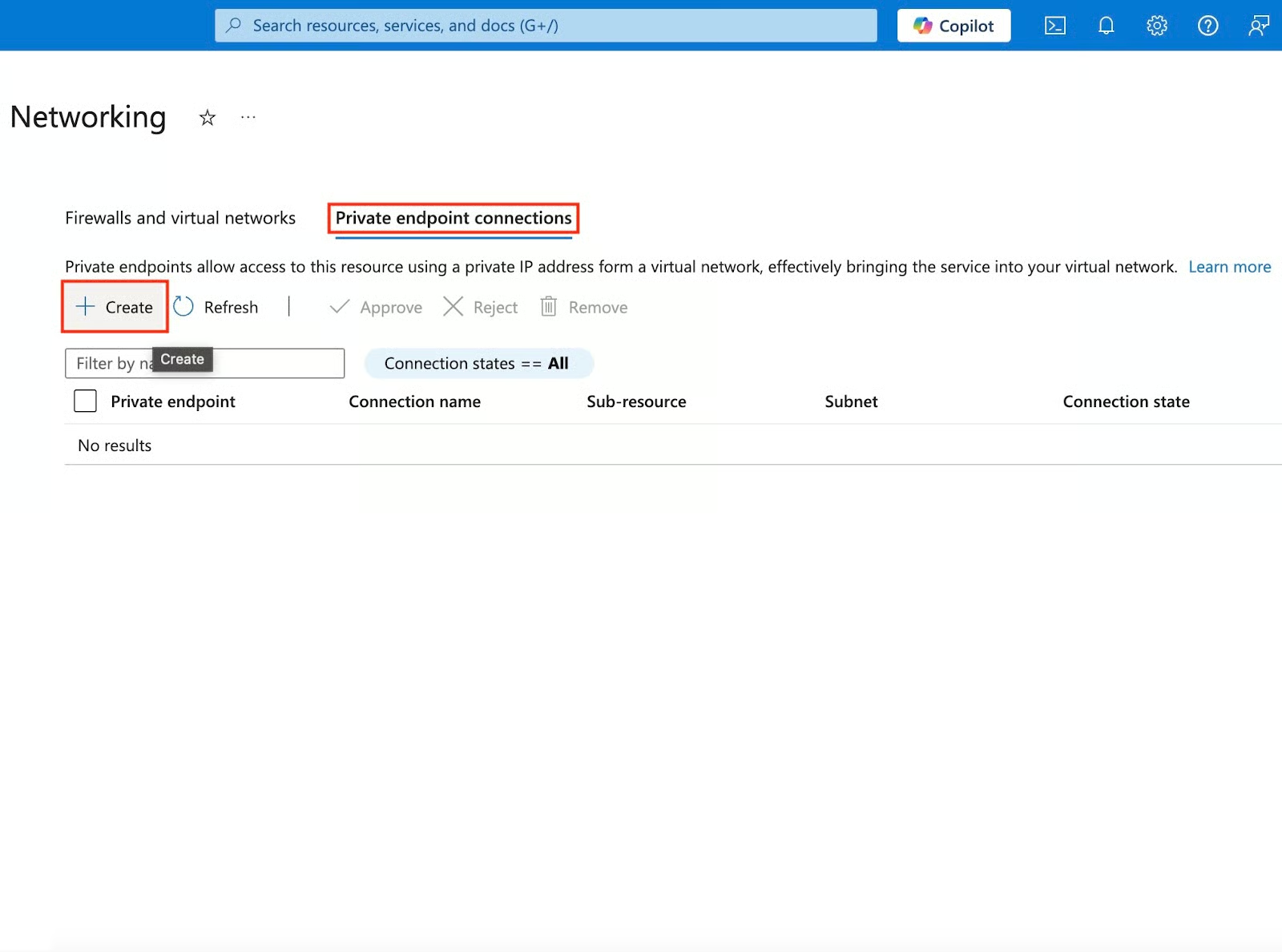
Moving forward, it's essential to keep these visual contexts in mind when discussing Wireless G Network Setup For Endpoint Security.
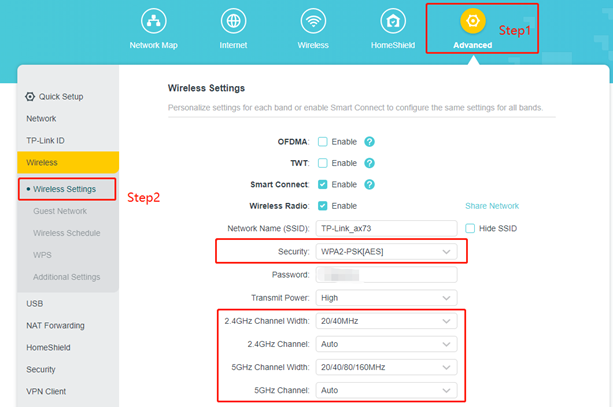
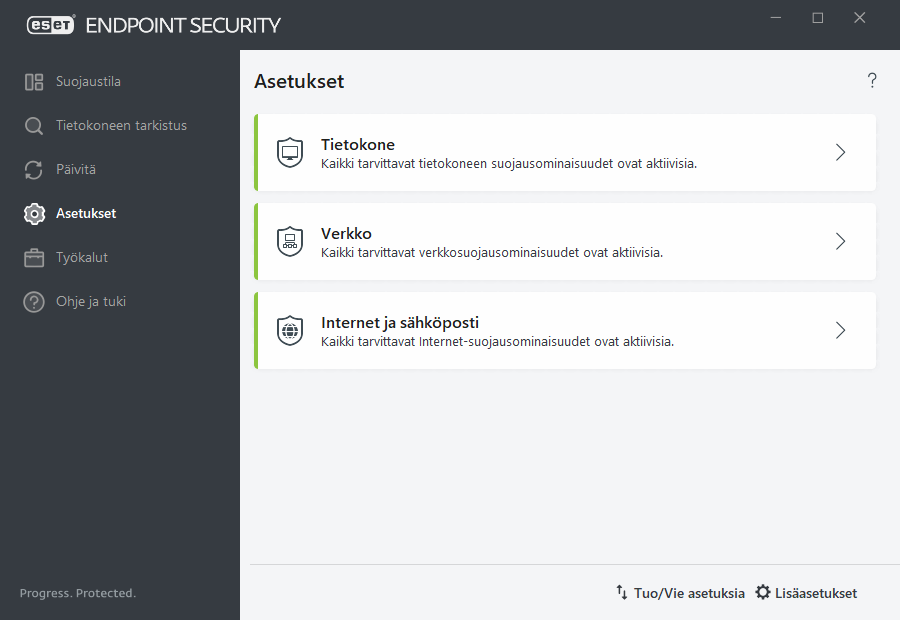
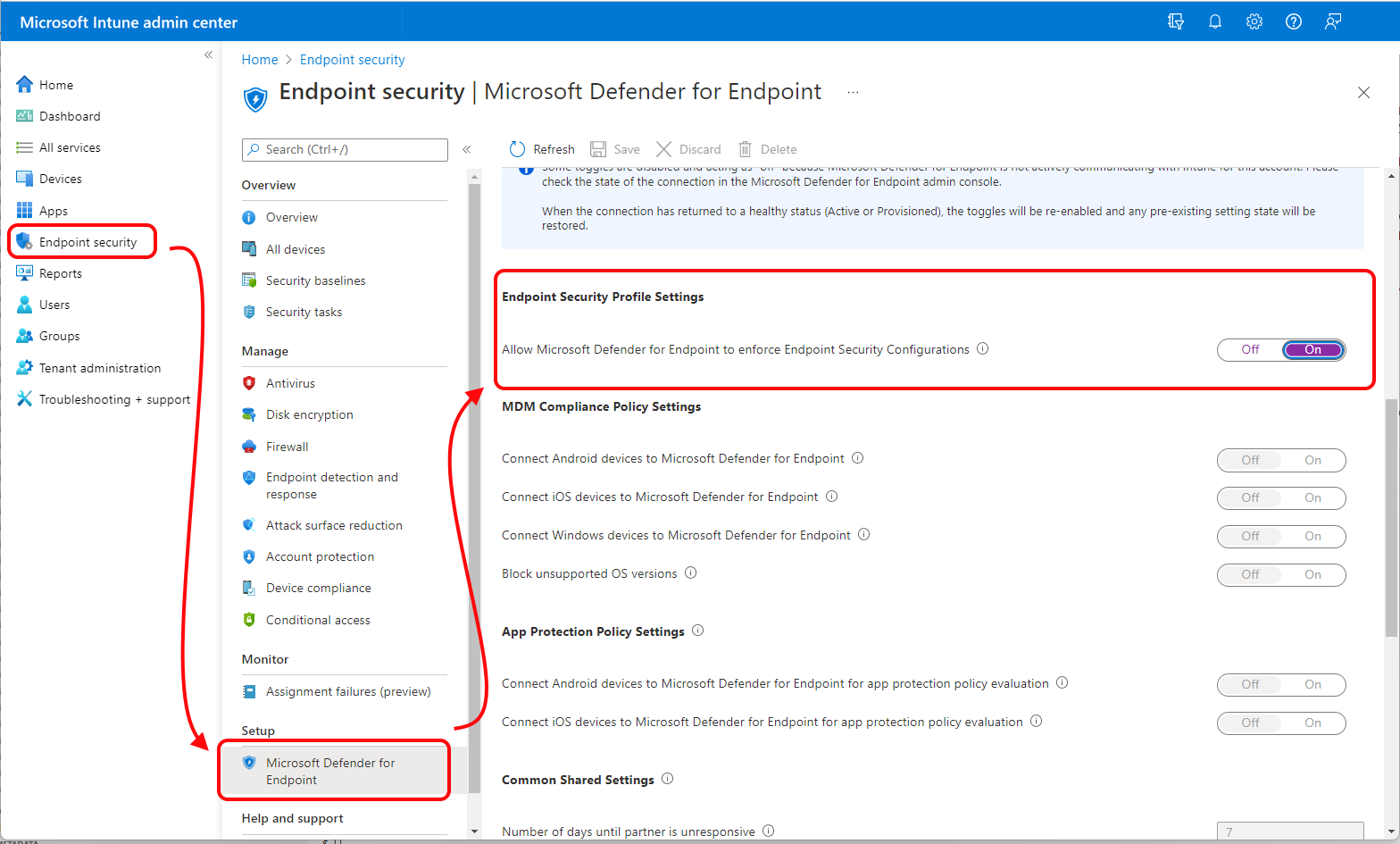
When setting up a Wireless G Network, consider the following best practices: * WPA3 is the most secure standard currently available * Select WPA2-Enterprise authentication if supported by the wireless AP and client network adapters * Implement a secure wireless network configuration, including WPA3 encryption and secure authentication methods * Regularly update and patch wireless network devices and firmware to prevent vulnerabilities Endpoint security management is essential in ensuring that all wired and wireless devices attempting to access a network meet corporate security policies. This involves: * Visibility: Unified insight into all endpoints for real-time monitoring and detection of unauthorized activities * Control: Automatic detection, isolation, and cleaning of infected or vulnerable endpoints * Continuous monitoring and response to emerging threats