Protecting the Future: A Comprehensive Guide on How to Secure Sensitive Data
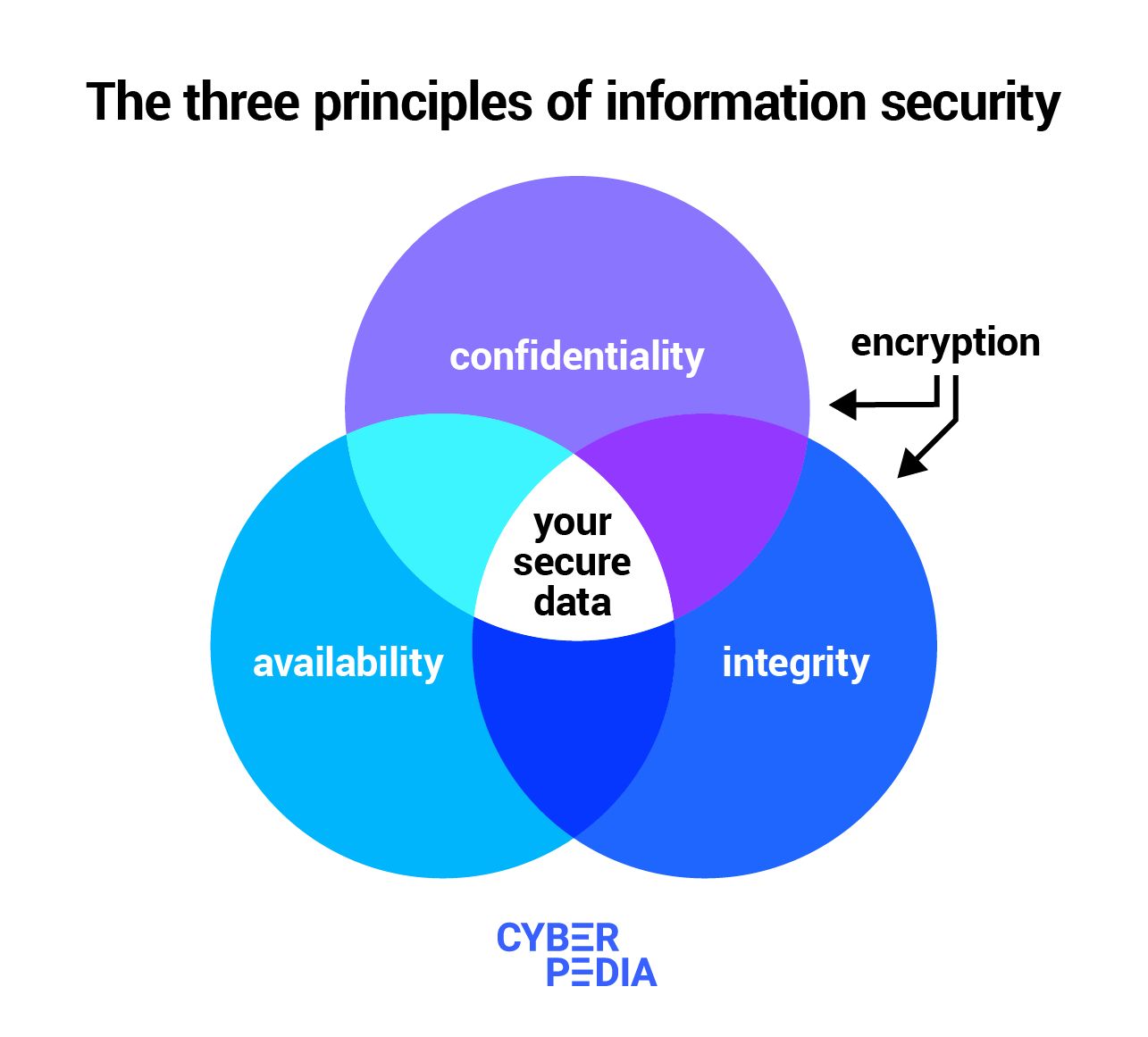
In today's digital age, safeguarding sensitive data has become an indispensable aspect of maintaining compliance, trust, and resilience against cyber threats. With the rise of data breaches and identity theft, it is crucial for individuals and organizations to implement robust strategies to prevent sensitive information from falling into the wrong hands. In this article, we will explore the importance of securing sensitive data, common data security threats, and provide actionable tips on how to safeguard sensitive information.What Qualifies as Sensitive Data?

This particular example perfectly highlights why How To Secure Sensitive Data is so captivating.
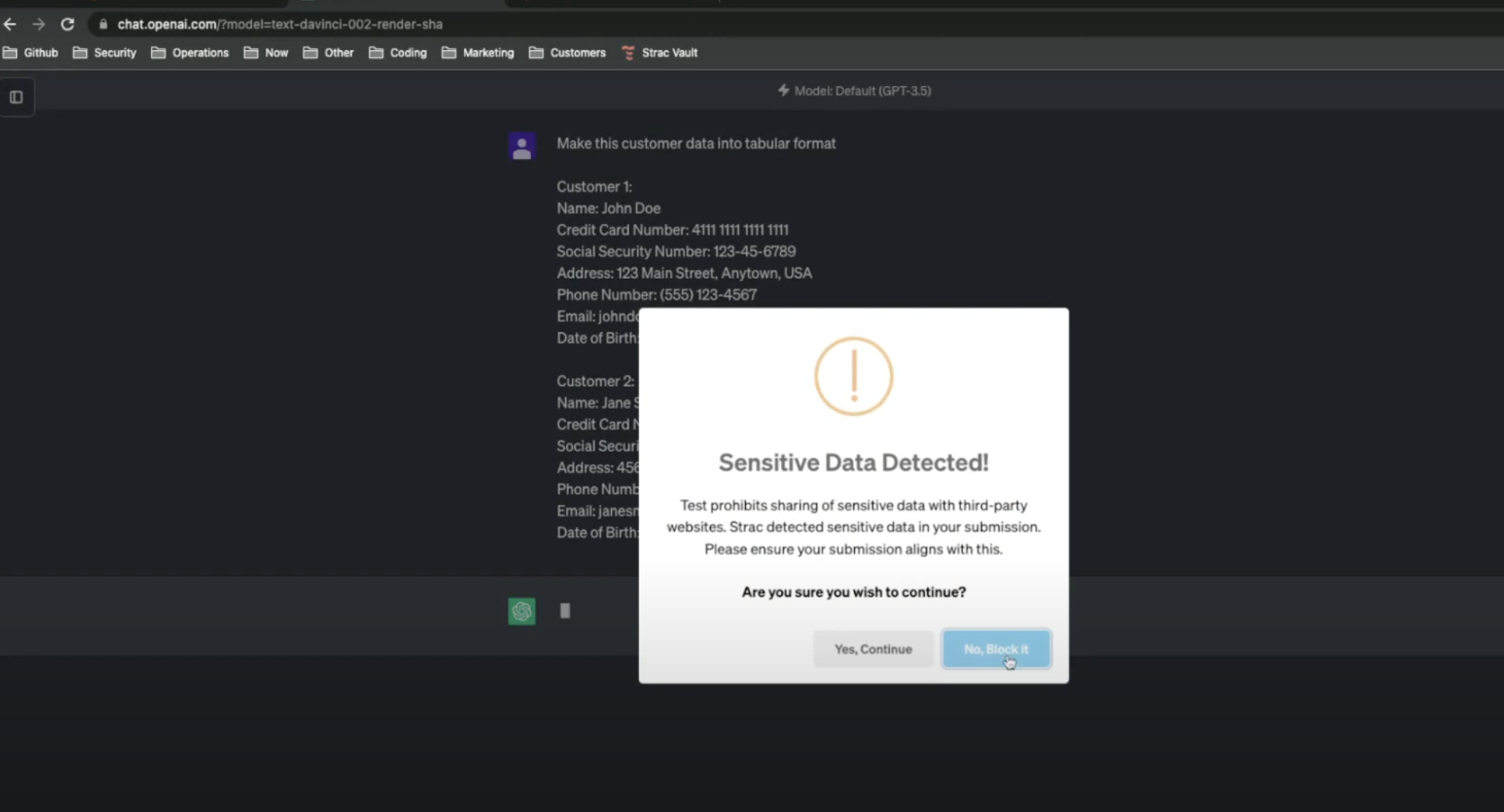
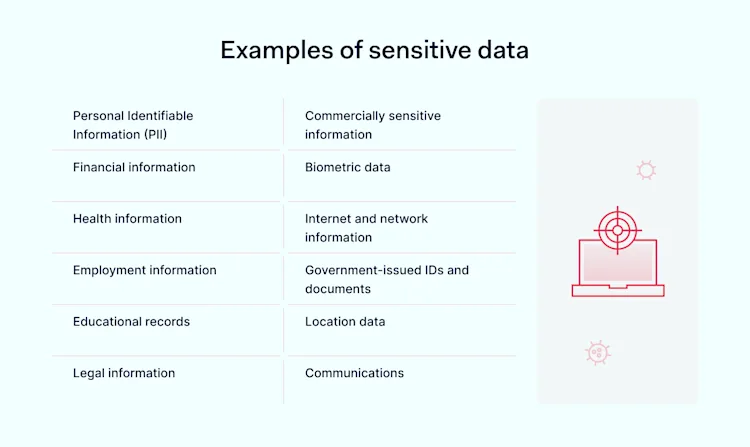
Sensitive data typically includes personally identifiable information (PII), such as names, addresses, social security numbers, financial information, and intellectual property. This type of data is attractive to hackers and malicious actors, who can use it for identity theft, financial fraud, or other illicit purposes. It's essential to recognize that sensitive data can be stored in various forms, including electronic and physical records, making it crucial to implement comprehensive security measures.Common Data Security Threats
As we can see from the illustration, How To Secure Sensitive Data has many fascinating aspects to explore.
Data breaches and cyber attacks are becoming increasingly common, with 3,322 cases reported in the United States in 2025, affecting over 278.83 million individuals. Some of the most common data security threats include: * **Phishing attacks**: Scammers use emails, texts, or phone calls to trick individuals into revealing sensitive information. * **Ransomware**: Malware that encrypts data and demands payment in exchange for the decryption key. * **Insider threats**: Authorized individuals with access to sensitive data intentionally or unintentionally compromise security. * **Data loss**: Physical or digital data is lost, stolen, or destroyed, compromising sensitive information.







.webp)