How to Protect Your Business: A Comprehensive Guide
As a business owner, you understand the importance of protecting your business from various threats. Whether it's cybercrime, data breaches, or physical security breaches, the consequences can be devastating. In this article, we will provide you with a comprehensive guide on how to protect your business, including cybersecurity best practices, intellectual property protection, and physical security measures.Secure Your Business
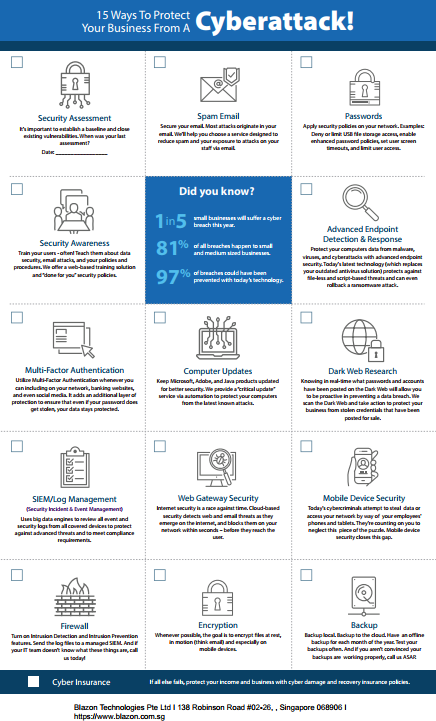
Your business is digitally connected to employees, vendors, and customers, making it a target for cybercriminals. According to a recent study, 60% of small businesses have been victims of cybercrime. To protect your business, you need to implement robust cybersecurity measures.Cybersecurity Best Practices
1. Password Management: Implement a password manager to generate and store unique, complex passwords for each employee. 2. Two-Factor Authentication:
Furthermore, visual representations like the one above help us fully grasp the concept of How To Protect Your Business.
Enable two-factor authentication to add an extra layer of security for login credentials. 3. Regular Software Updates: Ensure that all software, including operating systems, browsers, and applications, are updated regularly to patch security vulnerabilities. 4. Firewall Configuration: Configure firewalls to block incoming and outgoing traffic based on predetermined security rules. 5. Backup and Recovery: Regularly back up critical data and have a disaster recovery plan in place to minimize downtime in case of a data breach.Protect Your Business from Online Threats

Such details provide a deeper understanding and appreciation for How To Protect Your Business.
As a business owner, you need to be aware of the various online threats that can compromise your business. These include phishing attacks, malware, and ransomware. To protect your business from these threats, follow these best practices:Implement a Cybersecurity Policy
1. Develop a comprehensive cybersecurity policy that outlines security best practices, incident response procedures, and employee responsibilities. 2. Communicate the policy to all employees and ensure they understand their roles and responsibilities. 3. Regularly review and update the policy to ensure it remains effective and compliant with industry regulations.Protect Your Business from Intellectual Property Theft
Intellectual property (IP) theft can be devastating for businesses. To protect your business from IP theft, follow these best practices:Register Your Intellectual Property
1. Register your business name, logo, and trademarks with the relevant authorities to protect your brand identity. 2. Develop a comprehensive IP protection strategy that includes copyright and patent protection. 3. Regularly monitor your IP assets for potential infringement.Protect Your Business from Physical Security Threats

Moving forward, it's essential to keep these visual contexts in mind when discussing How To Protect Your Business.
Physical security threats can compromise your business's assets, including equipment, data, and employees. To protect your business from physical security threats, follow these best practices:



-p-800.jpg)














;)




