Cisco Router Configuration for IPS: A Comprehensive Guide
Introduction
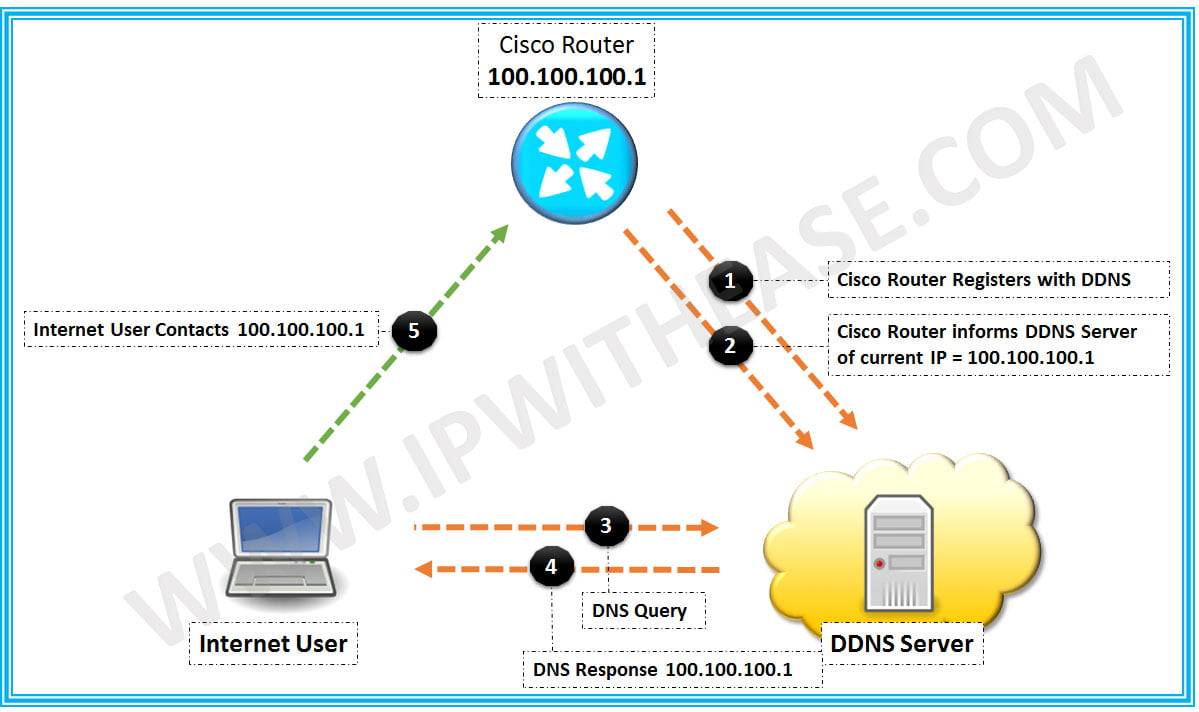
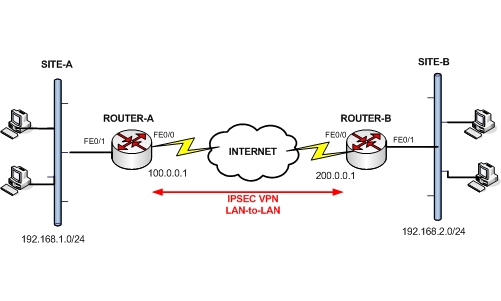
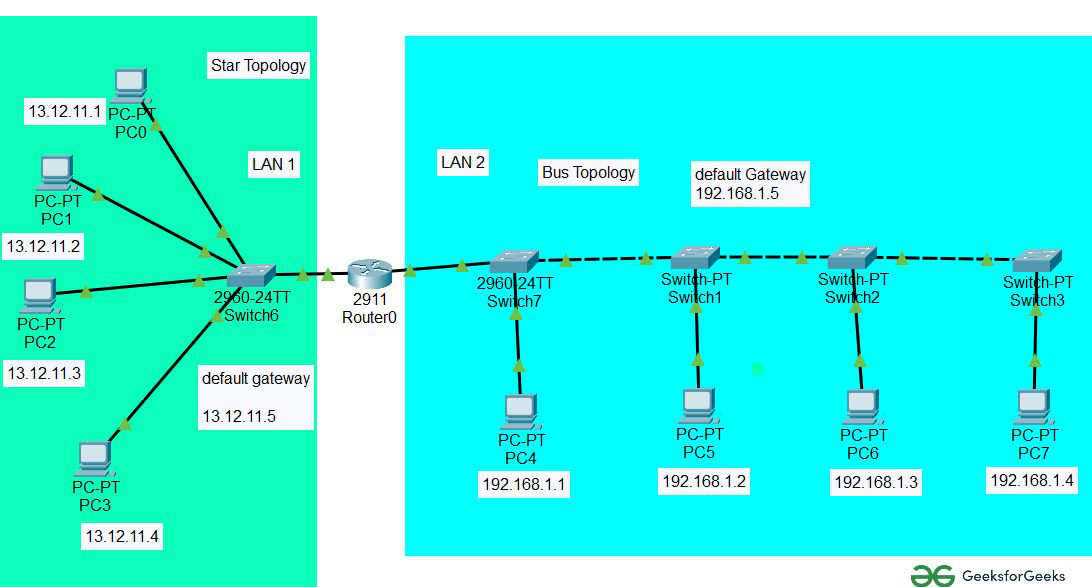
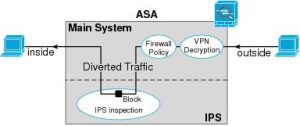
Configuring a Cisco router for IPS (Intrusion Prevention System) is a critical step in securing your network from potential threats. IPS technology is used to identify and prevent malicious traffic from entering your network, thereby safeguarding your sensitive data and systems. In this article, we'll provide a comprehensive guide on how to configure a Cisco router for IPS, covering the basics, advanced configurations, and best practices.Basic Router Configuration Example
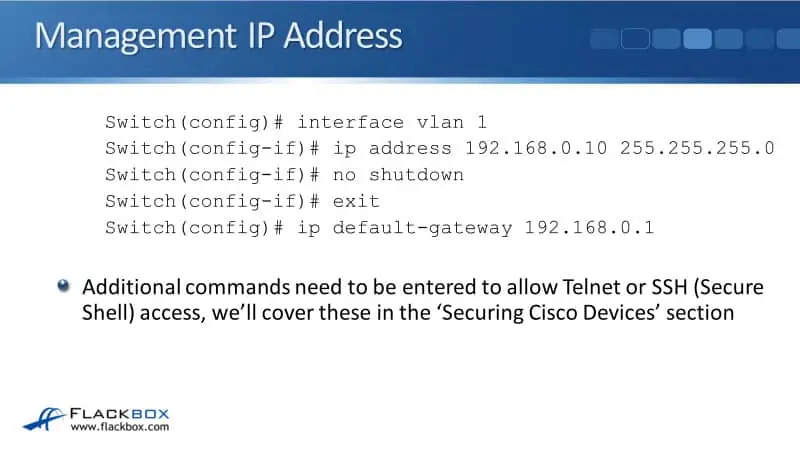
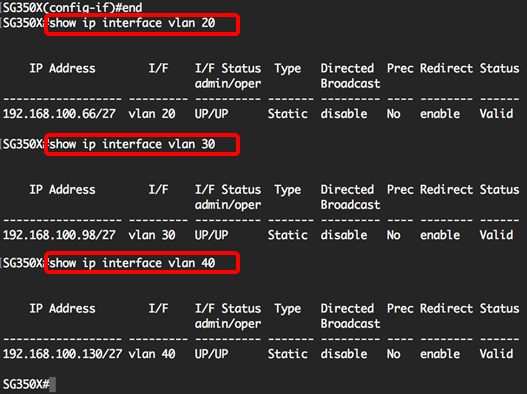
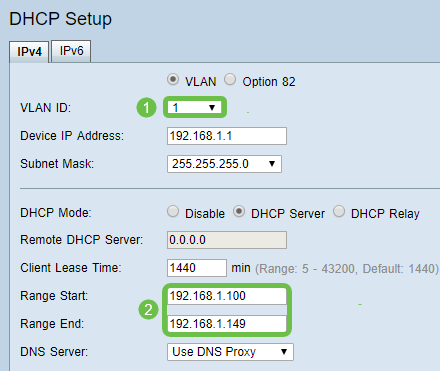
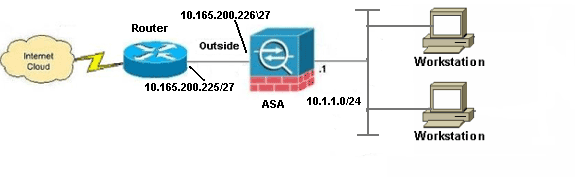
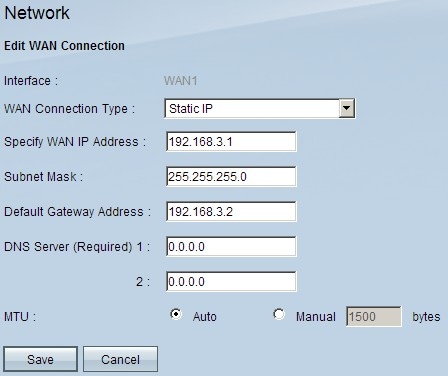
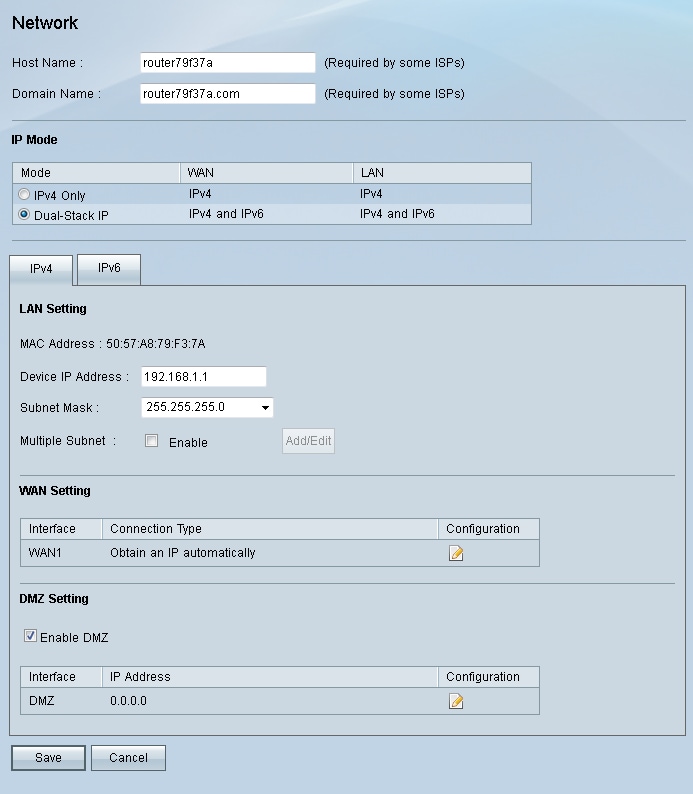
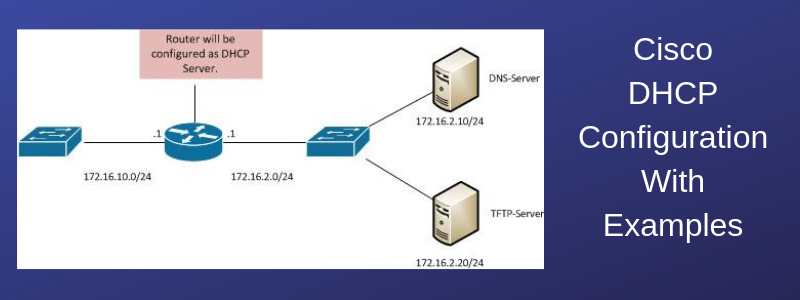
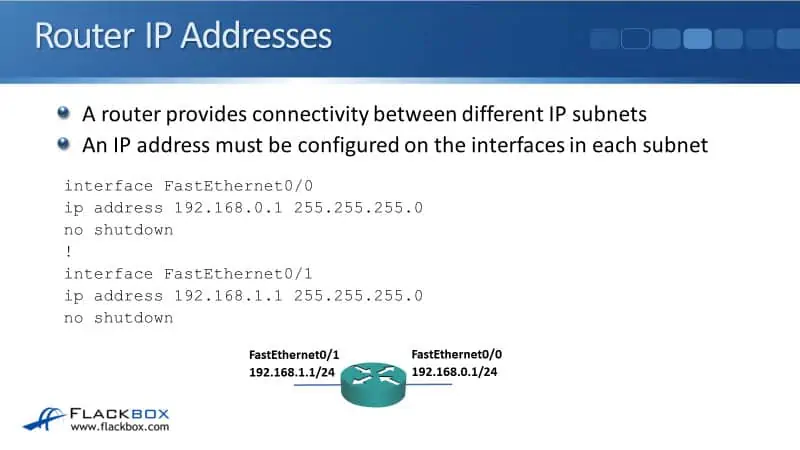
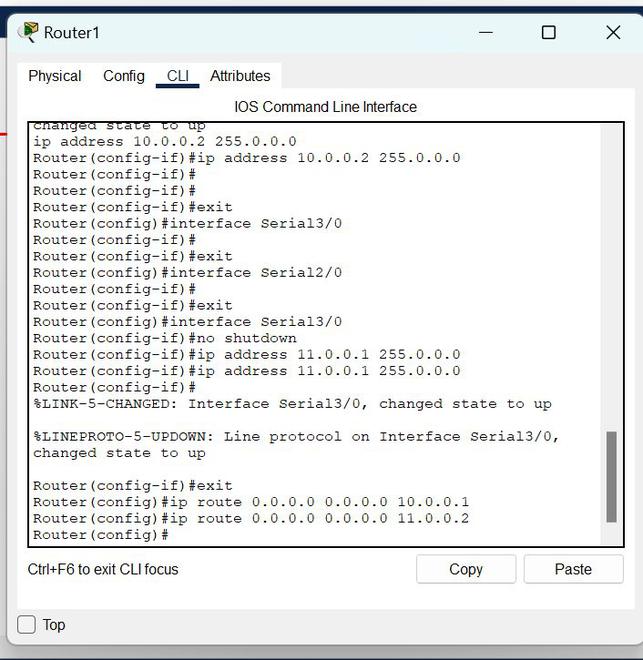
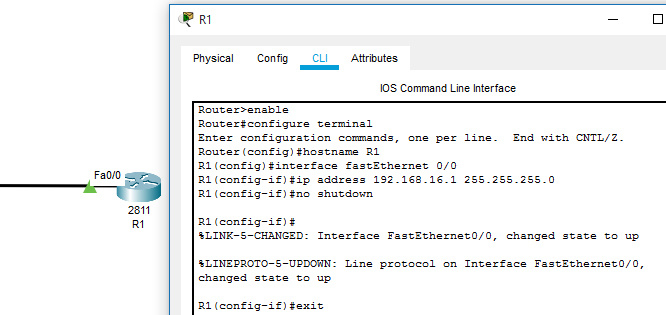
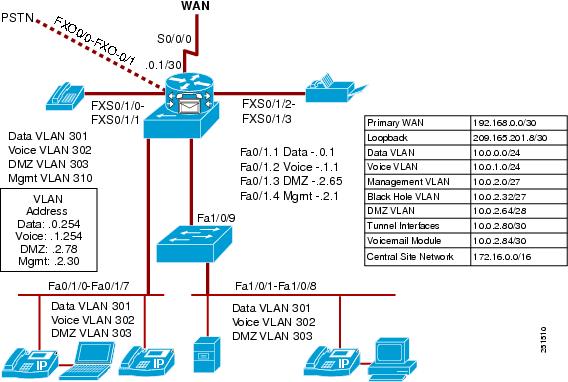
Before diving into IPS configuration, it's essential to understand the basic router configuration. The loopback interface, as shown in the following example, is used to support Network Address Translation (NAT) on the virtual-template interface. ```sql Router(config)# int loopback 0 Router(config-if)# ip address 200.200.100.1 255.255.255.0 ``` This configuration sets the loopback interface to 200.200.100.1 with a subnet mask of 255.255.255.0. The loopback interface acts as a static IP address to support NAT on the virtual-template interface.Configuring IPS on a Cisco Router
Advanced IPS Configuration
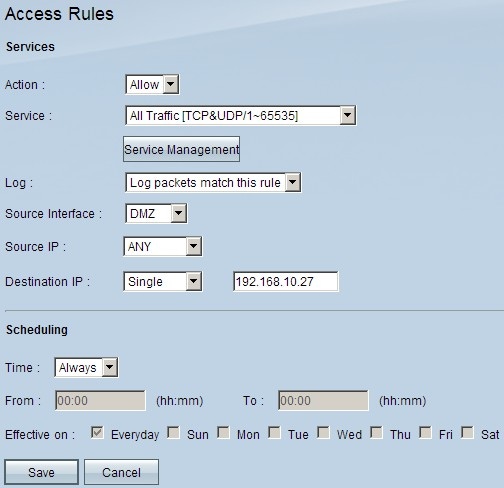
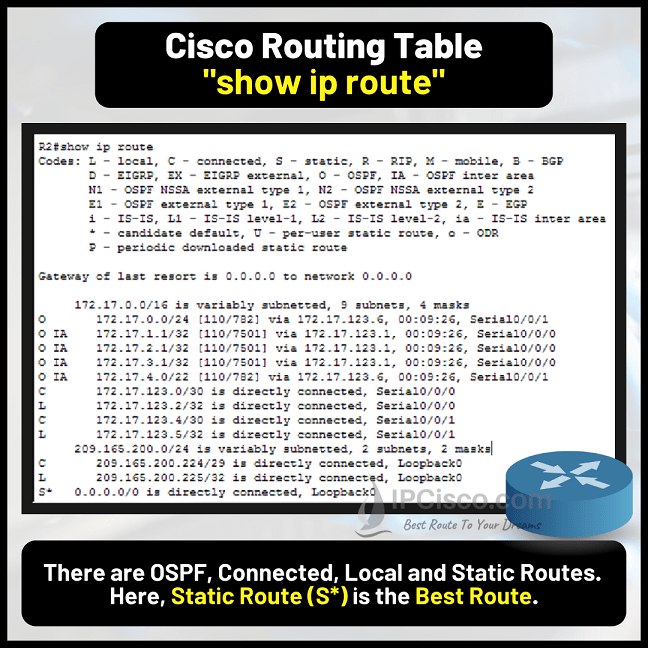
Advanced IPS configuration involves fine-tuning the IPS sensor settings to optimize its performance and effectiveness. Here are some key settings to consider: * **IPS policy version**: Determine the IPS policy version you are using (e.g., 7, 8, or 9) to ensure compatibility with your IPS sensor. * **URI**: Configure the uniform resource indicator (URI) of the device you want to secure. * **Access Groups**: Configure access groups to define which network traffic will be monitored by IPS.Best Practices
To ensure effective IPS configuration, follow these best practices: * **Regularly update your IPS signature database**: Regularly update your IPS signature database to ensure that your IPS sensor remains effective against emerging threats. * **Tune your IPS sensor settings**: Fine-tune your IPS sensor settings to ensure that they do not impact network performance. * **Use a combination of IPS technologies**: Use a combination of IPS technologies (packet sniffing, protocol analysis, file integrity checking, and port protection) to provide comprehensive security coverage.Conclusion