Errorfree Authorization Apparatus Strategy: Enhancing Security and Efficiency
Introduction
In today's digital landscape, ensuring secure access control is paramount. Organizations must implement robust authorization strategies to safeguard their sensitive information and protect against cyber threats. As technology continues to evolve, the complexity of authorization has grown, making it easier to get wrong. In this article, we will delve into the concept of an Errorfree Authorization Apparatus Strategy, exploring its benefits and implementation.Understanding Authorization
Authorization, a crucial aspect of identity and access management, verifies what a user or system can do within a given system. It follows authentication, which confirms the identity of the user or system. Proper authorization is essential to prevent unauthorized access and maintain data security.
Evolution of Authorization
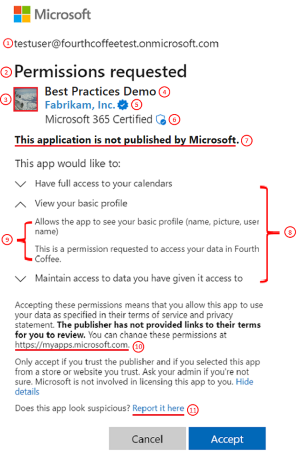
From simple UNIX permissions to complex distributed systems, authorization has evolved significantly. Recent failures at prominent tech companies like Facebook, Okta, and Microsoft highlight the importance of robust authorization strategies. These incidents can be attributed to errors in authorization implementation, which led to security breaches.
This particular example perfectly highlights why Errorfree Authorization Apparatus Strategy is so captivating.
Benefits of an Errorfree Authorization Apparatus Strategy
- Improved Data Security: With an Errorfree Authorization Apparatus Strategy, organizations can significantly reduce the risk of data breaches and cyber threats.
- Enhanced Efficiency: By streamlining authorization processes, organizations can improve user experiences and reduce latency. li>Flexibility and Scalability: An Errorfree Authorization Apparatus Strategy allows for easy integration with various technologies and systems.
- Compliance and Governance**: Organizations can ensure adherence to regulatory requirements and standards by implementing a robust authorization framework.
Implementing an Errorfree Authorization Apparatus Strategy
To implement an Errorfree Authorization Apparatus Strategy, organizations should follow these key steps:
1. Conduct a Thorough Risk Assessment
Identify potential security threats and vulnerabilities within the authorization process.
2. Develop a Comprehensive Authorization Framework
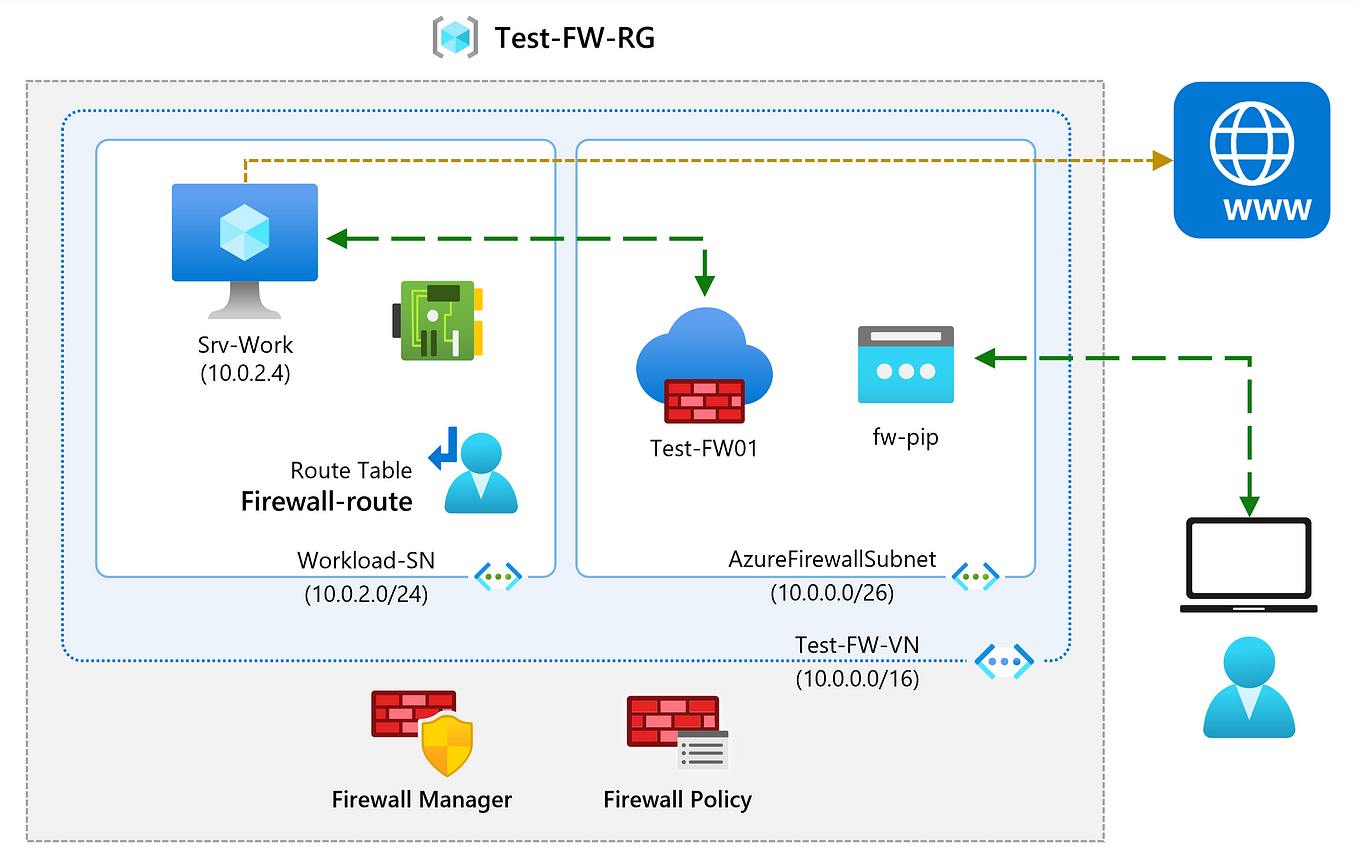
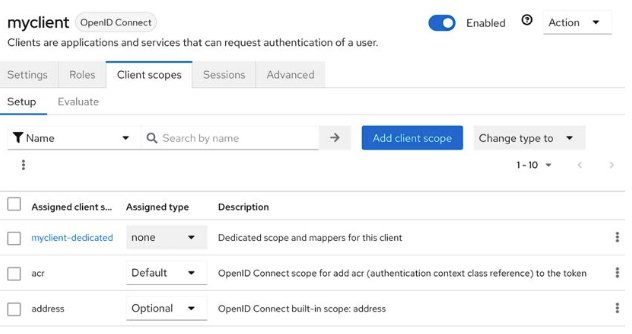
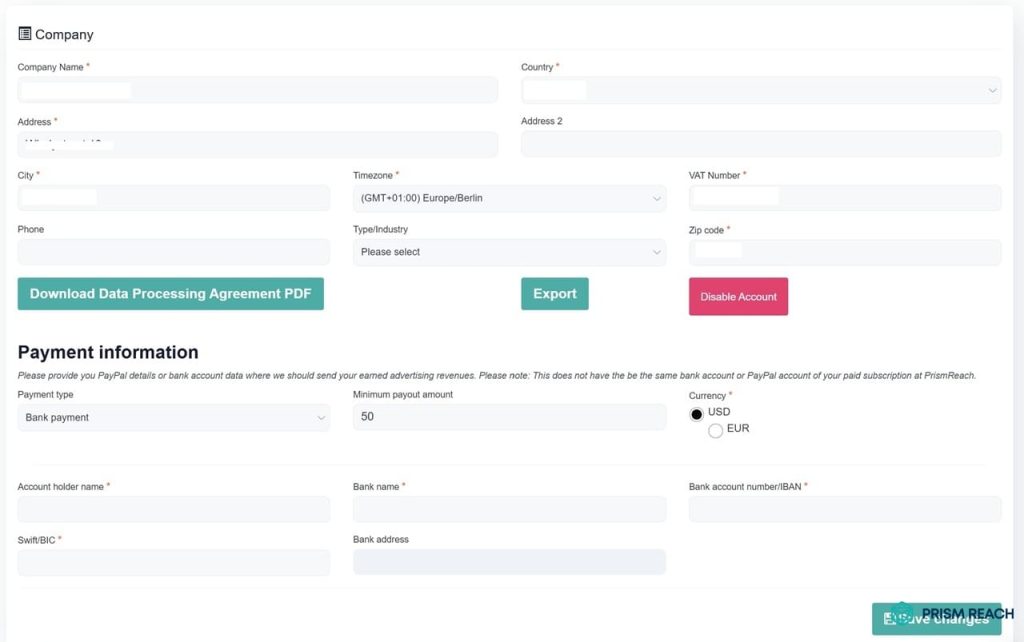
Establish a unified framework that incorporates various authentication and authorization technologies.
3. Implement Access Control Policies
Configure policies to govern access to sensitive resources and data.

4. Regularly Review and Update the Authorization Apparatus
Monitor and refine the authorization strategy to ensure continuous improvement and compliance.
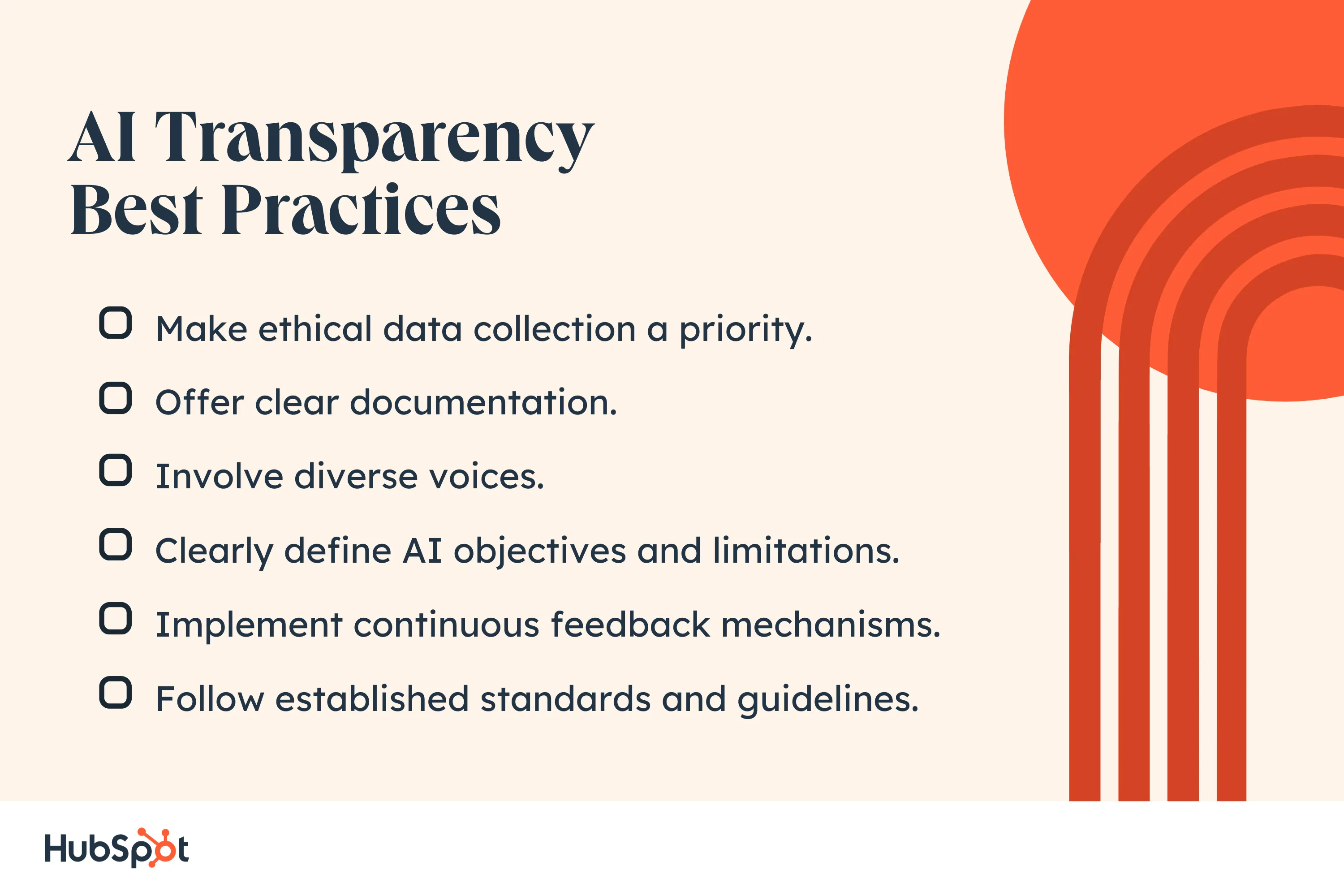
Best Practices for a Successful Errorfree Authorization Apparatus Strategy
- Employ a Zero Trust Architecture: Implement a Zero Trust approach to treat every user, device, and request as untrusted, even if they're inside the network.
- Integrate Multi-Factor Authentication: Utilize 2FA or MFA to add an extra layer of security and reduce the risk of unauthorized access.
- Conduct Regular Security Audits**: Monitor and assess the authorization framework on a regular basis to identify potential vulnerabilities and improve security.
- Develop a Comprehensive Compliance Plan**: Ensure adherence to regulatory requirements and industry standards by establishing a robust compliance program.